Database
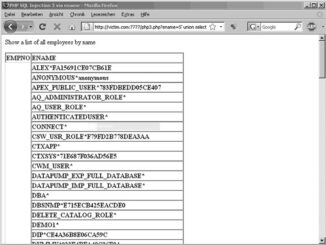
Exploiting SQL Injection : Stealing the Password Hashes
We briefly talked about hashing functions earlier in this chapter, when we discussed a successful attack that recovered the passwords of the application users. In this section, we’ll talk about hashes again, this time regarding […]